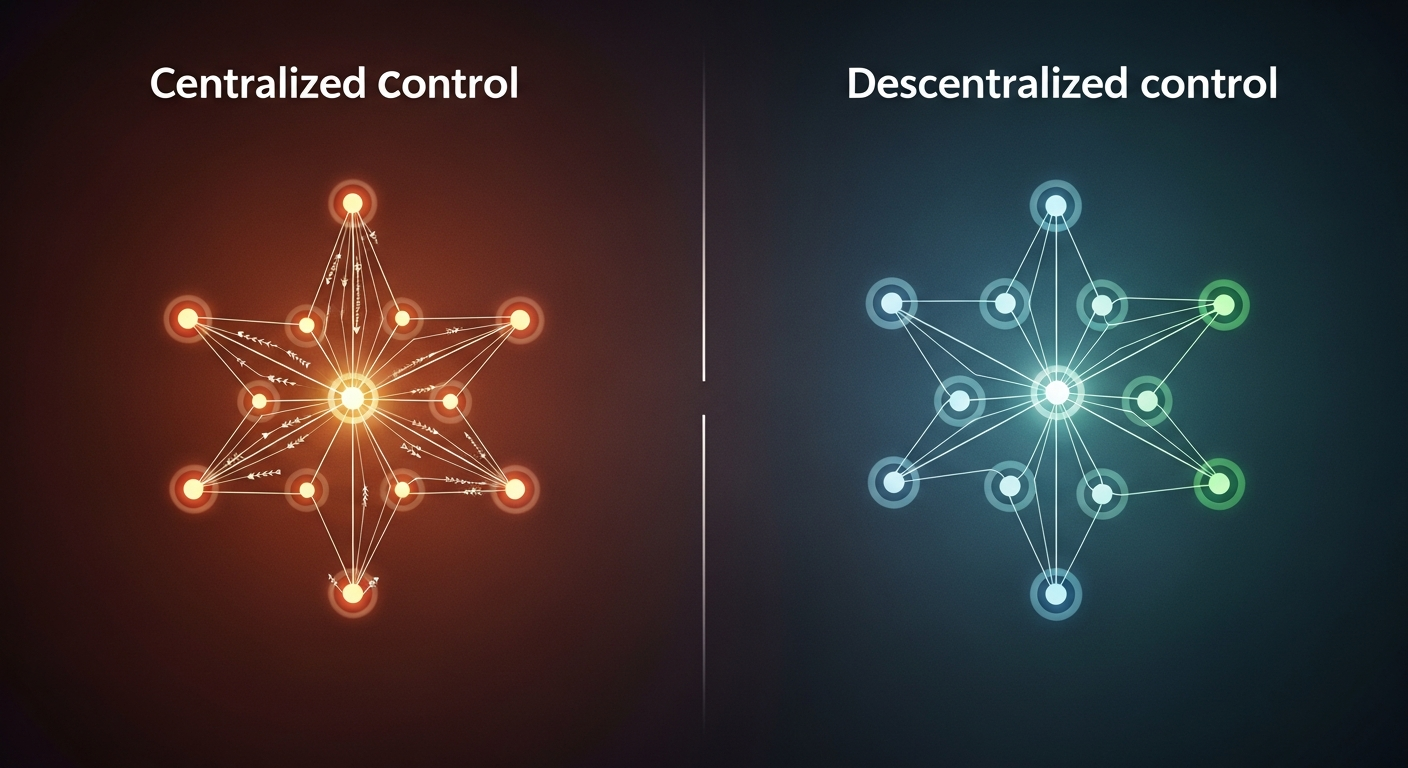
In the vast and intricate landscape of technology and organizational design, a fundamental question often arises that dictates the very fabric of how systems operate: Centralized vs. Decentralized Control. This isn’t just an abstract theoretical debate for engineers and academics; it’s a practical, strategic decision with profound implications for everything from software architecture and network infrastructure to corporate governance and global supply chains. The choice between a single point of command and a distributed network of autonomous nodes can impact efficiency, security, scalability, and resilience. As an expert content writer and SEO specialist, my goal is to peel back the layers of this critical dichotomy, exploring the core characteristics, advantages, disadvantages, and real-world applications of both centralized and decentralized architectures. By the end of this comprehensive guide, you’ll have a clearer understanding of which architecture might be better suited for different contexts, enabling you to make informed decisions in a world increasingly reliant on robust and adaptable systems.
Understanding Centralized Control Architectures
A centralized control architecture is perhaps the most intuitive and historically prevalent model for organizing systems. At its core, it signifies a structure where a single entity, point, or authority holds the primary responsibility for decision-making, resource allocation, and overall management. Think of a traditional monarchy, a corporate hierarchy with a CEO at the helm, or a classic client-server application where all data and processing reside on one main server. This model emphasizes order, efficiency through clear command, and ease of oversight.
Definition and Core Characteristics
In a centralized system, there is a distinct, identifiable central node or authority. This node processes requests, manages resources, stores data, and dictates the flow of information. All other participants or components in the system communicate directly with this central authority. Key characteristics include:
- Single Point of Authority: One entity or server makes all critical decisions and controls the system’s state.
- Hierarchical Structure: Information and commands flow predominantly from top-down.
- Data Cohesion: All data is typically stored in a single, unified database or repository, ensuring consistency.
- Centralized Management: Administration, updates, and maintenance are handled from one location.
- Examples: Traditional client-server applications, mainframe computing, many legacy IT systems, conventional banking systems, and most governmental structures.
Advantages of Centralized Systems
Despite its perceived limitations in a rapidly evolving digital world, centralized control offers compelling benefits that make it suitable for numerous applications:
- Simplicity and Ease of Management: With a single point of control, system design, implementation, and maintenance are often less complex. Troubleshooting is streamlined as there’s a clear locus of issues.
- Consistent Data and State: All components rely on a single, authoritative data source. This inherently leads to strong data consistency, as there’s no need for complex synchronization protocols between multiple nodes.
- Easier Security Implementation: Securing a single, well-defined point is often simpler than securing a multitude of distributed nodes. Resources can be focused on hardening one critical area, making it easier to monitor and audit.
- Faster Decision-Making: In systems where rapid top-down decision-making is paramount, a centralized authority can act quickly without needing to achieve consensus across multiple independent entities.
- Lower Initial Setup Cost: For smaller-scale projects or specific applications, the initial investment in hardware and infrastructure for a centralized system can be lower than setting up a distributed network.
- Predictable Performance: Performance characteristics can be more easily predicted and managed since all requests are routed through a known pathway.
Practical Tip: Centralized architectures shine when high consistency, tight control, and rapid, authoritative decision-making are paramount. They are often ideal for smaller-scale applications, systems with stringent regulatory compliance requirements, or tasks where absolute data integrity from a single source is non-negotiable, such as traditional financial ledgers or national defense systems.
Disadvantages of Centralized Systems
However, the strengths of centralized systems often give rise to their most significant weaknesses:
- Single Point of Failure (SPOF): The most critical drawback is that if the central node fails, the entire system can become inoperable. This poses a significant risk to availability and business continuity.
- Scalability Challenges: As demand grows, the central node can become a bottleneck. Scaling often involves upgrading the central server (vertical scaling), which has physical limits and diminishing returns, unlike the horizontal scaling offered by distributed systems.
- Security Vulnerabilities: While easier to secure in some respects, the central node becomes a highly attractive target for attackers. A successful breach can compromise the entire system, leading to catastrophic data loss or system manipulation.
- Lack of Resilience: Centralized systems are inherently less resilient to disruptions, whether from hardware failure, software bugs, or external attacks. Recovery can be time-consuming and expensive.
- Censorship and Control Risks: The central authority has absolute power, which can lead to issues of censorship, lack of transparency, or misuse of power, especially in social or political contexts.
- Network Latency: Users geographically distant from the central server may experience higher latency, impacting performance and user experience.
Exploring Decentralized Control Architectures
In contrast to the hierarchical nature of centralized systems, decentralized control architectures distribute authority, processing, and data across multiple independent nodes or participants. There is no single master controller; instead, nodes cooperate to achieve system goals, often through peer-to-peer communication and consensus mechanisms. This model is inspired by natural systems and has gained significant traction with the advent of technologies like blockchain, cloud computing, and microservices.
Definition and Core Characteristics
A decentralized system operates without a single orchestrating entity. Instead, various components or nodes interact directly with each other. Key characteristics include:
- No Single Point of Control: Authority and decision-making are distributed among many participants.
- Distributed Consensus: Agreement on the system’s state or actions is often achieved through a consensus mechanism (e.g., Proof of Work in Bitcoin) rather than a central decree.
- Redundancy and Replication: Data and functionality are often replicated across multiple nodes, ensuring high availability and fault tolerance.
- Peer-to-Peer Interaction: Nodes communicate directly with each other, rather than exclusively through a central hub.
- Examples: Blockchain networks (Bitcoin, Ethereum), peer-to-peer file-sharing systems (BitTorrent), modern cloud-native microservices architectures, Distributed Autonomous Organizations (DAOs), and the Internet itself.
Advantages of Decentralized Systems
Decentralized architectures offer powerful advantages, especially in environments demanding high availability, trust, and scalability:
- Resilience and Fault Tolerance: The absence of a single point of failure means the system can continue to operate even if several nodes fail. Redundancy ensures that functions and data are available elsewhere.
- Enhanced Scalability: Decentralized systems can often scale horizontally by adding more nodes to the network. This distributes the workload and avoids bottlenecks more effectively than vertical scaling.
- Improved Security and Attack Resistance: There is no single attractive target for attackers. Compromising a decentralized system would require simultaneous attacks on many nodes, making it significantly more difficult and expensive.
- Censorship Resistance: Without a central authority to impose controls, it’s much harder for any single entity to censor information or control access within the network. This is a core tenet of many blockchain applications.
- Transparency and Immutability (e.g., Blockchain): In certain decentralized systems like blockchains, all transactions and data changes are publicly verifiable and immutable, fostering trust among participants.
- Autonomy for Participants: Individual nodes or users have greater autonomy and less reliance on a central intermediary, leading to more open and permissionless systems.
Practical Tip: Decentralized architectures excel in environments requiring high availability, resistance to censorship, trust minimization among unknown parties, and massive scalability. They are particularly well-suited for global networks, public utilities, and applications where data integrity and user autonomy are paramount, such as cryptocurrencies and distributed ledgers.
Disadvantages of Decentralized Systems
While powerful, decentralization comes with its own set of challenges:
- Increased Complexity in Design and Management: Designing, implementing, and maintaining a decentralized system is inherently more complex due to the need for distributed consensus, data synchronization across multiple nodes, and intricate network management.
- Slower Decision-Making (Consensus Overhead): Reaching consensus across a large number of nodes can be a time-consuming process, leading to slower transaction finality or decision-making compared to a centralized authority.
- Potential for Inconsistent Data/State: Achieving absolute, immediate data consistency across all nodes in a large decentralized system is challenging and often leads to concepts like “eventual consistency.” Conflicts can arise and need robust resolution mechanisms.
- Higher Operational Overhead/Cost: While initial setup might be distributed, the ongoing operational costs can be significant due to the need for more hardware (multiple nodes), increased network traffic for synchronization, and specialized expertise for management.
- Governance Challenges: Establishing effective governance and upgrade mechanisms in a decentralized system can be notoriously difficult, as there’s no single entity to enforce changes.
- Security Concerns (Individual Node Vulnerabilities): While the overall system is resistant to attack, individual nodes might be easier to compromise. Securing all nodes effectively can be a challenge.
- Resource Intensive: Many decentralized systems (especially those using Proof of Work) require significant computational and energy resources to maintain security and consensus.
Key Considerations for Choosing the Right Architecture
The choice between centralized and decentralized control is rarely black and white. It hinges on a careful evaluation of specific project requirements, constraints, and long-term goals. Here are critical factors to consider:
Scalability Requirements
How much growth do you anticipate? If rapid, massive growth is expected, a decentralized architecture with its ability for horizontal scaling might be more suitable. If the system’s size is relatively stable or scales vertically (e.g., a single powerful server), centralized might suffice. Consider the trade-off between the complexity of distributed scaling versus the limits of vertical scaling.
Security and Resilience
What is your tolerance for downtime or data loss? If 24/7 availability and extreme fault tolerance are critical, the inherent redundancy of a decentralized system provides a stronger foundation. If your threat model involves sophisticated, targeted attacks on single points, decentralization’s distributed nature offers better resistance. For less critical systems, the simpler security of a centralized model might be sufficient.
Cost and Resource Management
Evaluate both initial setup costs and long-term operational expenses. Centralized systems can have lower initial costs for smaller setups, but scaling can become expensive. Decentralized systems might have higher initial complexity and resource demands (e.g., energy consumption for blockchain mining), but they can offer cost efficiencies at scale through commodity hardware. Consider the availability of expertise; decentralized systems often require more specialized skills.
Performance and Latency
Does your application require real-time processing with minimal latency? Centralized systems can sometimes offer lower latency if users are geographically close to the server, as communication paths are direct. Decentralized systems, particularly those relying on complex consensus mechanisms, can introduce higher latency due to the need for network propagation and agreement among nodes. However, edge computing approaches can bring computation closer to users in decentralized models.
Data Consistency and Integrity
How critical is immediate and absolute data consistency? Centralized systems naturally excel here. Decentralized systems often trade immediate consistency for availability and partition tolerance (the CAP theorem), leading to eventual consistency. Understand your application’s requirements for data integrity; some applications can tolerate slight delays in consistency, while others cannot.
Governance and Decision-Making Structure
Who needs to make decisions, and how quickly? If a clear, hierarchical command structure is desired for swift decisions, centralized is superior. If collective decision-making, transparency, and resistance to single-party control are important (e.g., for community-driven projects), decentralized governance mechanisms (like DAOs) are more appropriate, albeit slower.
Practical Tip: Many modern systems are not purely one or the other but rather adopt hybrid models. Consider which parts of your system need stringent central control (e.g., user authentication, core business logic) and which can benefit from distribution (e.g., content delivery, processing large datasets, microservices).
Real-World Applications and Hybrid Approaches
Understanding the theoretical differences is one thing; seeing them in action truly illuminates their trade-offs. Both centralized and decentralized architectures power critical aspects of our digital world, and increasingly, we see a blending of the two.
Centralized Examples
Many systems we interact with daily are predominantly centralized:
- Traditional Banking Systems: A bank’s internal ledger is highly centralized, with a single database maintaining all customer account balances and transaction records. This ensures absolute consistency and compliance.
- Cloud Computing (in essence): While cloud services like AWS, Google Cloud, or Azure offer distributed *resources*, the underlying control, billing, and management of these resources are centralized within each provider’s infrastructure. Users interact with a central API and control plane.
- Social Media Platforms: Companies like Facebook (Meta), X (formerly Twitter), and Instagram maintain centralized control over user data, content moderation, and platform features. This allows for unified user experiences but also raises concerns about data privacy and censorship.
- Flight Control Systems: Air traffic control operates on a highly centralized model to ensure safety and prevent collisions, where a central authority directs all aircraft in a given airspace.
These systems prioritize consistency, security through a single perimeter, and the ability for a single entity to enforce rules and make rapid decisions.
Decentralized Examples
Decentralization has given rise to revolutionary new systems and approaches:
- Blockchain and Cryptocurrencies (Bitcoin, Ethereum): These are the quintessential examples of decentralized networks. There’s no central bank or authority; instead, transactions are verified and recorded by a network of independent nodes, ensuring censorship resistance, transparency, and immutability.
- Peer-to-Peer (P2P) File Sharing (BitTorrent): Users share files directly with each other, rather than downloading from a central server. This dramatically improves download speeds and reduces the load on any single server.
- The Internet’s Domain Name System (DNS): While having root servers, the overall DNS system is distributed, with many independent servers managing different parts of the domain name space, ensuring resilience.
- Cloud-Native Microservices Architectures: Modern application development often breaks down monolithic applications into many small, independent services (microservices) that communicate over a network. While often orchestrated by central tools, the services themselves can operate in a highly distributed fashion, improving scalability and fault tolerance.
These systems thrive where trust among participants is low, resilience is paramount, and censorship resistance is a core feature.
The Rise of Hybrid Models
Increasingly, the most effective architectures are not purely centralized or decentralized but rather strategic hybrids that leverage the strengths of both. This allows organizations to optimize for specific needs without falling victim to the rigid limitations of either extreme.
- Content Delivery Networks (CDNs): A website’s core server is centralized, but its static content (images, videos) is cached and delivered by a decentralized network of edge servers globally. This reduces latency and improves performance for users worldwide.
- Edge Computing: Data is often processed closer to its source (the “edge”) in decentralized nodes (e.g., IoT devices, local servers), reducing latency and bandwidth usage. However, this localized data is often aggregated and analyzed in a centralized cloud for broader insights and management.
- Distributed Databases with Centralized Query Layers: Many modern database systems offer distributed storage for scalability and resilience, but a centralized query engine or API might provide a unified interface for applications, simplifying data access.
- Modern Enterprise IT: Enterprises might have a centralized Active Directory for identity management, but their applications run on a distributed microservices platform, deployed across multiple cloud regions, with a mix of centralized and decentralized logging and monitoring.
Actionable Advice: When designing a hybrid system, start by identifying the core, mission-critical components that demand absolute consistency and control (these might be centralized). Then, look for peripheral services or data processing tasks that can benefit from distributed resilience, scalability, and autonomy (these can be decentralized). Carefully define the interfaces and communication protocols between these central and distributed elements to maintain coherence and manage complexity.
Conclusion
The debate between centralized and decentralized control architectures is not about finding a universally “better” solution, but rather understanding the intricate trade-offs inherent in each. Centralized systems offer simplicity, strong consistency, and efficient top-down control, making them ideal for applications demanding high regulatory compliance, small-scale operations, or situations where rapid, authoritative decision-making is paramount. However, they come with significant risks related to single points of failure, scalability limitations, and potential censorship.
Conversely, decentralized systems provide unparalleled resilience, scalability, and censorship resistance, making them suitable for global networks, public utilities, and applications where trust minimization and user autonomy are critical. Yet, they introduce complexities in design, management, slower decision-making processes, and potential governance challenges.
As technology continues to evolve, the trend clearly points towards sophisticated hybrid models. These architectures strategically combine elements of both centralized and decentralized control to harness their respective strengths while mitigating their weaknesses. The optimal choice ultimately depends on a deep understanding of your specific requirements: the desired level of scalability, security posture, performance needs, data consistency demands, and the governance model that best suits your goals. By carefully weighing these factors, designers and organizations can construct robust, efficient, and future-proof systems capable of thriving in an increasingly dynamic and interconnected world.
